Bridging Zero Trust Gaps in Isolated Industrial Networks
Bridging Zero Trust Gaps in Isolated Industrial Networks
The traditional industrial security model is built upon a single, uncompromising principle: isolation. For decades, the "air gap" has been the gold standard for protecting operational technology (OT) from the volatile threats of the public internet. However, as modern industry moves toward a future defined by artificial intelligence, predictive maintenance, and real-time analytics, this isolation has created an unintended and dangerous paradox. The very walls built to protect industrial assets are now the primary bottleneck for the data movement required to optimize them.
When data cannot move securely across network boundaries, operations teams are forced to find workarounds. Statistics now suggest that a staggering 84% of leadership teams recognize that cross-network data sharing is their most significant security risk, yet more than half of all organizations still rely on manual transfers—often referred to as "sneakernet"—to bridge these gaps. Whether it is a technician carrying a USB drive into a cleanroom or a manual file transfer through a temporary laptop connection, these gaps in the Zero Trust framework represent the single largest attack vector in the modern industrial enterprise.
To solve this, the industry must move beyond the binary choice of total isolation or total exposure. The solution lies in a post-quantum Zero Trust architecture that treats every data movement as a highly authenticated, cryptographically shielded event. This is where the integration of network-level security and industrial data planes becomes the new standard for infrastructure resilience.
The Failure of the Physical Air Gap
The physical air gap is no longer the fortress it once was. In fact, it often creates a false sense of security that masks significant vulnerabilities. Because the network is perceived as "isolated," internal security controls are frequently more relaxed than those on the corporate side. This means that if an attacker successfully bridges the gap via a manual transfer or a compromised vendor device, they find themselves in an environment with broad lateral movement opportunities and minimal internal verification.
Zero Trust is often discussed in the context of remote users accessing cloud applications, but its most critical application is in the machine-to-machine (M2M) communication that occurs across isolated industrial segments. A true Zero Trust framework assumes that the breach has already occurred or is imminent. It dictates that network access alone can no longer be trusted; instead, identity must be verified continuously, and data movement must be restricted to the absolute minimum required for the task.
The bottleneck occurs because traditional Zero Trust Network Access (ZTNA) solutions were not built for the complexities of OT. They often struggle with industrial protocols like OPC UA or the high-reliability requirements of a factory floor. This forces a choice: weaken security to allow data to flow, or maintain isolation and lose the benefits of data-driven insights.
Conflux and the Meta Air Gap
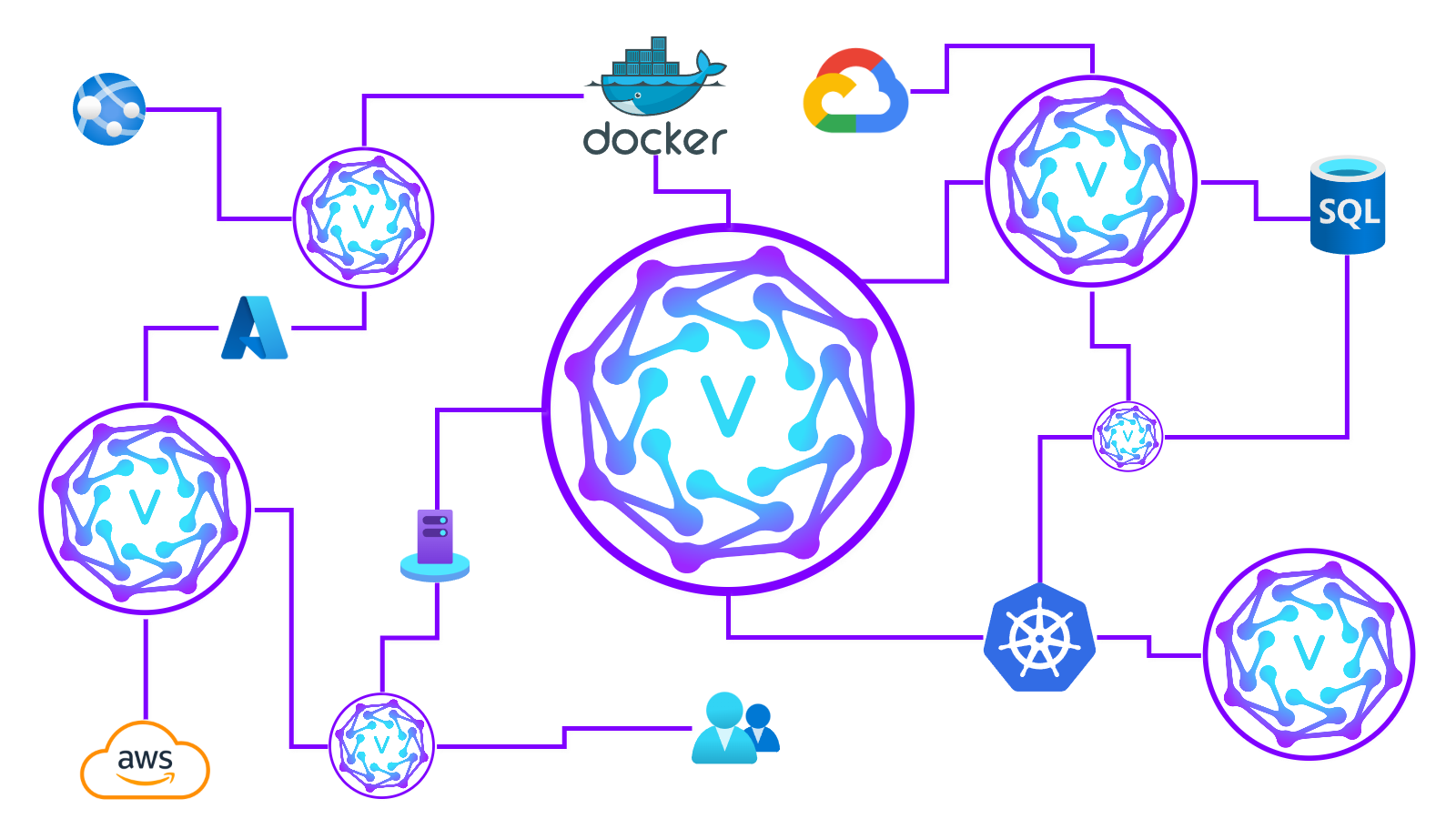
Bridging this gap requires a new architectural approach known as the Meta Air Gap. Unlike a traditional VPN, which extends a network and often grants broad access once a tunnel is established, a Meta Air Gap uses an identity-authenticated mesh to create precise, ephemeral paths for data.
VeilNet Conflux serves as the foundation for this architecture. It functions as a secure post-quantum network connector that replaces the broad, vulnerable tunnels of the past with a high-integrity mesh. In a Conflux-driven environment, no device is visible to the network until it has been rigorously authenticated. This "black cloud" approach ensures that the industrial attack surface is virtually invisible to unauthorized actors.
The technical brilliance of Conflux lies in its quantum-resistant packet routing. As we enter the era of quantum computing, traditional encryption methods are at risk of "harvest now, decrypt later" attacks, where adversaries steal encrypted data today with the intent of breaking it once quantum processors become viable. By utilizing post-quantum cryptography (PQC) at the network layer, Conflux future-proofs industrial data movement, ensuring that even the most sensitive telemetry remains secure for decades to come.
This meta air gap provides the benefits of physical isolation—denying broad connectivity—while allowing for the fluid, secure movement of authenticated packets. It eliminates the need for manual transfers by providing a programmable, secure conduit that can be strictly governed by policy.
Aether and the Industrial Data Plane
Connectivity is only half of the equation. Once a secure path is established by Conflux, the data itself must be handled in a way that respects the specialized requirements of industrial environments. This is the role of the industrial data plane.
VeilNet Aether sits above the Conflux network layer, acting as the real-time engine for industrial integration. While Conflux handles the "where" and "how" of secure routing, Aether handles the "what" of the data flow. It is designed specifically to interface with the protocols that drive modern industry, including OPC UA, RESTful APIs, and the Model Context Protocol (MCP).
In a typical scenario, an OT engineer may need to pull telemetry from a PLC (Programmable Logic Controller) on a factory floor and push it to an AI-driven analytics engine in a secure cloud environment. Using Aether, that data is ingested via OPC UA, wrapped in the post-quantum protection of the Conflux mesh, and delivered to its destination via a secure RESTful API or MCP integration.
This end-to-end integration removes the friction that usually leads to security exceptions. Because Aether understands industrial protocols, it can perform granular inspection and policy enforcement on the data itself, ensuring that only the specific required telemetry is moved, rather than opening a broad port that could be exploited. This level of micro-segmentation at the protocol level is what allows Zero Trust to finally succeed in the OT space.
Eliminating the Manual Transfer Risk
By combining Conflux and Aether, organizations can finally retire the "sneakernet." The risks associated with manual transfers—malware on USB drives, human error in file handling, and the lack of an audit trail—are replaced by a fully automated, cryptographically verified system.
Every data movement event in the VeilNet ecosystem is tied to a specific identity and governed by a centralized policy engine. This provides CISOs and OT engineers with something they have never had before: total visibility and control over the data moving between their most sensitive network segments. If an anomaly is detected, the mesh can automatically sever the specific path without impacting the rest of the operation.
Furthermore, this architecture supports the "Assume Breach" mentality by ensuring that even if one segment of the network is compromised, the attacker cannot pivot to other segments. The identity-authenticated nature of the mesh means that a compromised credential or device only grants access to the specific, limited resources defined in its policy, and nothing more.
A Secure Path Toward Industrial AI
The push for AI in manufacturing and infrastructure is relentless, but AI is only as good as the data it consumes. For many organizations, the data movement bottleneck has been the primary inhibitor of AI adoption. Security teams, rightfully concerned about the risks of connecting isolated networks to AI stacks, have often been the "department of no."
With a post-quantum Zero Trust platform, security becomes an accelerator rather than a roadblock. By providing a secure, automated way to move industrial data from the edge to the AI engineering stack, VeilNet enables organizations to innovate with confidence. The combination of Conflux’s secure routing and Aether’s protocol-aware data plane ensures that as the volume of tokens and requests grows, the security posture remains unshakeable.
The transition from traditional, perimeter-based security to a decentralized, identity-centric model is no longer optional. As industrial networks become more complex and the threats against them more sophisticated, the air gap must evolve. By embracing the Meta Air Gap and the industrial data plane, enterprises can bridge the Zero Trust gap, eliminate the risks of manual data movement, and secure their operations for the post-quantum age.
Bridging the Air Gap with Identity Centric Post Quantum Mesh Networking
Discover how VeilNet Conflux and Aether secure legacy OT environments against quantum threats while enabling seamless IT-OT integration through zero trust.
Building Post Quantum Zero Trust for Modern Industrial Environments
Discover how VeilNet's Conflux and Aether solve the challenges of OT Zero Trust, eliminating lateral movement and securing legacy industrial infrastructure.