Post-Quantum Zero Trust, Built Into the Network Layer
Zero Trust Enforced On Every Packet, Not Just Connections
VeilNet replaces IP-based routing with cryptographic identity. Every packet is authenticated with post-quantum signatures before it reaches your application -- no VPN, no proxy, no hardware replacement. Deploys as software on your existing infrastructure in minutes.
Secure with Extreme Performance
VeilNet uses multi-agent reinforcement learning to optimise routing dynamically. Performance scales with the network rather than degrading as complexity increases.
1ms Overhead
High-performance Golang concurrent crypto, routing operations with in-memory loadbalancing.
Unlimited Bandwidth
Aggregated WebRTC data channels as one data link, as fast as your network allows.
Idenpendent Tunnels
Each destination has its own "Tether" tunnel, independent of others. No competition, no queueing overhead, no waiting for slow sinks.
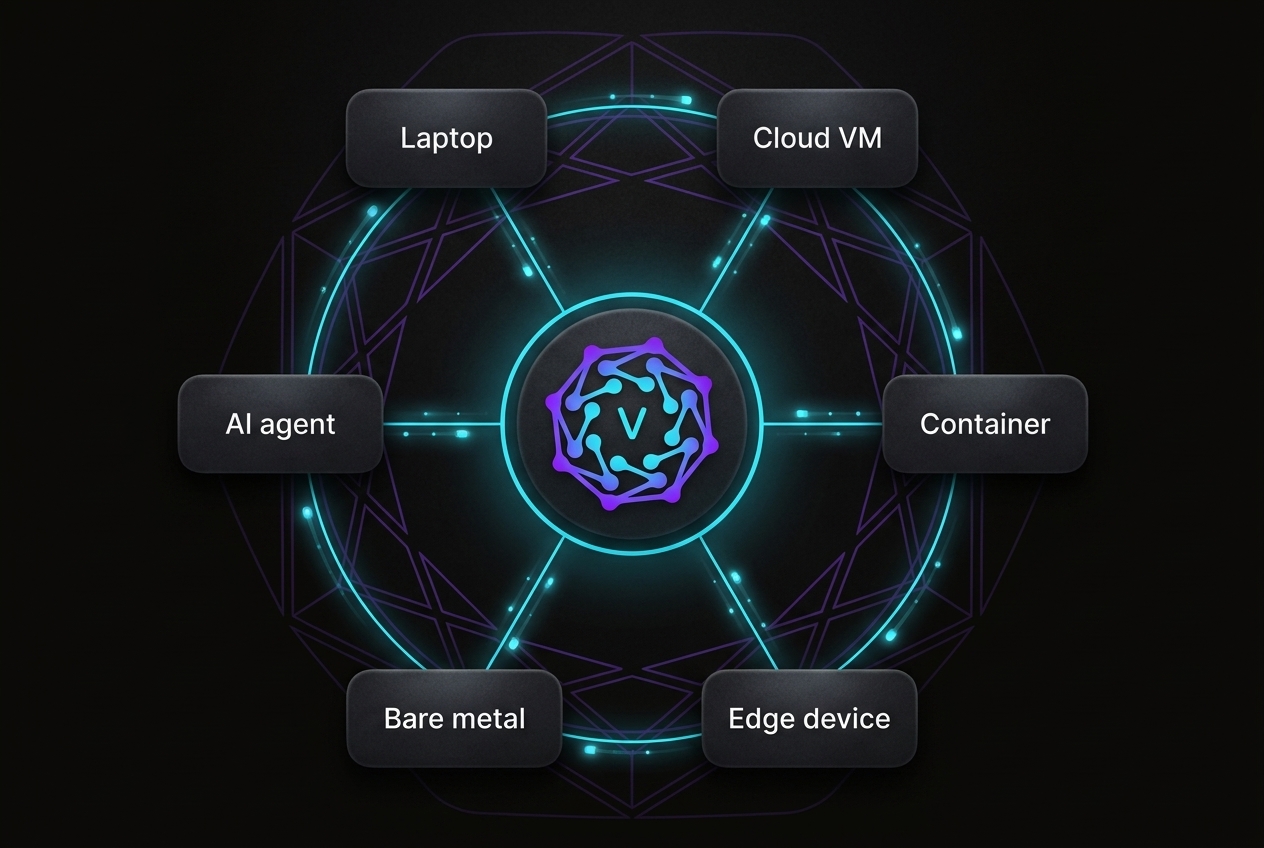
Connect anything, from anywhere
No open ports. No relay. No exposure on Internet.
VeilNet routes by cryptographic identity, not IP address. Cloud VMs, containers, bare-metal servers, edge devices, and AI agents connect into one private fabric the moment Conflux starts -- no firewall rules, no inbound ports, no shared relay infrastructure.
Tailscale trusts everything inside the tunnel. ngrok and Cloudflare route your traffic through their infrastructure. VeilNet has no trusted interior and no shared relay -- your data never leaves your control.
Cloud, on-prem, containers, edge, OT, IT -- one fabric
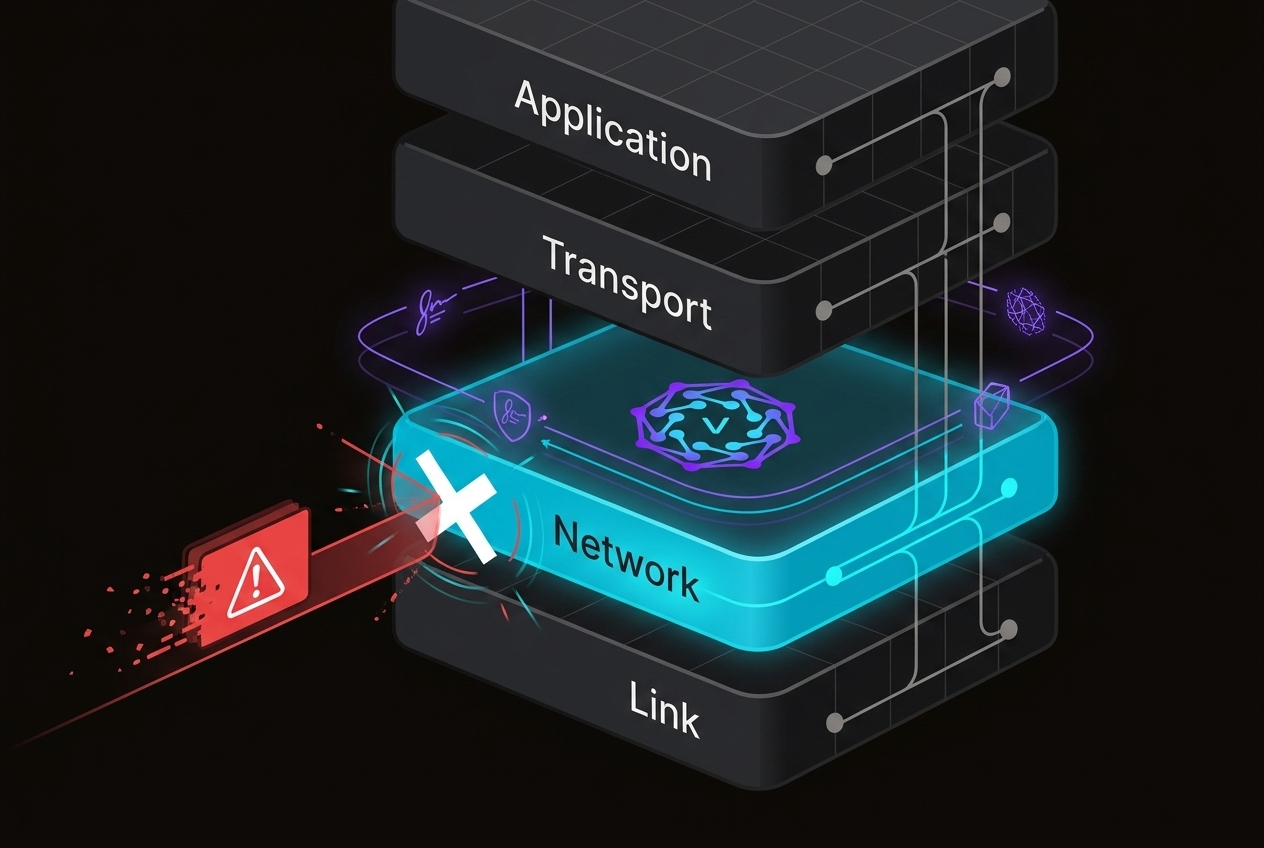
Zero-day proof
A vulnerability is unreachable if the packet never arrives.
Every packet must carry a valid ML-DSA signature before it reaches your application. No valid identity -- no delivery, regardless of what the packet carries. There are no IPs to scan, no ports to probe, and no topology to enumerate.
Traditional firewalls block known signatures and pass everything else through. VPNs trust all traffic inside the tunnel. VeilNet makes unauthenticated traffic invisible at the network layer -- before it reaches any application.
Per-packet ML-DSA authentication stop zero-day attacks before they happen
Post-quantum today, not 2030
Compliant before every deadline -- software only, nothing replaced.
ASD mandates quantum-safe critical systems by 2028. NSA CNSA 2.0 requires quantum-resistant infrastructure by 2026. Tailscale and WireGuard use Curve25519 -- not post-quantum.
VeilNet deploys as software on your existing infrastructure, implementing ML-KEM-1024 and ML-DSA-65 at NIST FIPS 203 and 204. No firmware changes, no hardware replacement, no downtime. Quantum-safe from day one.
ML-KEM and ML-DSA, align with NIST FIPS 203 and 204

How it works
- Authenticate With Your Existing Identity ProviderAgents and services authenticate via your OAuth2 provider -- Google, Okta, Entra ID, or any OIDC-compatible IdP. No new credentials, no API keys to rotate.
- Connect Across Any Network AutomaticallyConflux nodes establish direct post-quantum encrypted connections automatically, even behind NAT, firewalls, and across cloud providers. No VPN configuration, no firewall rules.
- Enforce Access at the Network LayerDefine policies like "Agent A can reach Database B." Everything else is unreachable by default at the network layer -- not blocked by a rule, simply not routable.
- Self-Healing RoutingWhen routes fail or nodes go offline, the network reconverges automatically using multi-agent reinforcement learning. No manual intervention, no BGP reconfiguration.
- Multi-Path RedundancyConflux aggregates multiple WebRTC data channels per path. Direct connections when latency allows, automatic multi-hop routing when needed -- without falling back to a single proxy.
- Quantum-Safe From Day OneVeilNet uses ML-KEM-1024 and ML-DSA-65 (NIST FIPS 203 and 204). Your infrastructure is compliant with post-quantum mandates without a future migration.
- Full Observability With OpenTelemetryEvery control-plane action is traced and streamed to your existing OpenTelemetry-compatible observability stack -- no new monitoring tools, no additional agents.
- Fully Self-Hosted, No Cloud DependencyEvery VeilNet component runs on your own infrastructure. No shared control plane, no vendor-managed nodes, no data leaving your environment.
- One Function Call to IntegrateDevelopers integrate VeilNet with a single SDK call. No waiting for firewall change requests or infrastructure provisioning.
Join the waitlist
Be among the first to experience VeilNet enterprise features
Frequently Asked Questions
Direct answers to the questions we hear most from security, infrastructure, and operations teams.