VeilNet - The Future-Ready Zero Trust Network Architecture
VeilNet: The Future-Ready Zero Trust Network Architecture
Executive Summary
Enterprise network security faces converging threats that render traditional solutions inadequate: autonomous AI agents are projected to outnumber human workers 82 to 1 by 2026, quantum computing threatens to decrypt today's encrypted traffic within the decade, and legacy VPN/ZTNA architectures collapse under the weight of modern scale requirements. VeilNet addresses these challenges through three breakthrough innovations that deliver immediate business value:
Business Impact:
- Infrastructure cost reduction through elimination of VPNs, proxies, service meshes, and complex firewall management
- Improved system availability via self-healing architecture that automatically routes around network failures
- Future-proof security investment with quantum-resistant cryptography meeting multiple jurisdictions' quantum-resistance mandates
- Linear scaling complexity supports unlimited growth without the quadratic cost penalties of mesh networks
- Faster deployment compared to traditional SASE/ZTNA implementations
Technical Foundation:
VeilNet fundamentally reimagines secure network communications by abandoning the mathematical constraints of peer-to-peer mesh topologies, eliminating vulnerabilities inherent in tunnel-level authentication, and implementing quantum-resistant cryptography at the network layer. This white paper provides comprehensive technical analysis of VeilNet's architecture, direct comparisons with leading ZTNA solutions (Tailscale, Twingate, Netbird), and detailed use cases demonstrating applicability to both emerging AI-agent ecosystems and traditional enterprise infrastructure modernisation.
Why Current ZTNA Solutions Fail at Scale
Contemporary ZTNA solutions promise simplified security but introduce hidden operational costs and scalability barriers that compound as your organisation grows. Understanding these limitations is essential for evaluating long-term network infrastructure investments and avoiding expensive technology dead-ends.
The Application-Layer Authentication Trap:
When traditional ZTNA solutions prove inadequate, enterprises often compound the problem by layering additional authentication systems at the application level—implementing API gateways, Web Application Firewalls (WAFs), identity-aware proxies, and service mesh authorisation policies. This horizontal expansion of security controls creates a brittle, complex architecture where each application requires independent security configuration, multiple authentication handshakes occur for single transactions, and security policies fragment across dozens of disparate systems.
This approach fundamentally fails because it attempts to solve a network-layer trust problem with application-layer patches. Each additional authentication layer introduces new failure points, increases latency, and expands the attack surface through additional API endpoints and authentication tokens. Security teams must now maintain authentication logic across every application, coordinate policy changes across multiple systems, and troubleshoot failures that span network, proxy, and application layers.
The Strategic Challenge:
Current ZTNA vendors offer two fundamentally flawed architectural approaches, each creating distinct business risks:
- Mesh Networks (Tailscale, Netbird): Connection requirements grow quadratically with each added device, creating exponential database overhead, delayed policy updates, and eventual system collapse at enterprise scale. For organisations planning AI agent deployments, this architecture becomes economically and operationally unfeasible.
- Centralised Proxies (Twingate): All traffic routes through mandatory chokepoints, degrading performance, creating single points of failure, and requiring constant manual policy management. This model cannot support bidirectional machine-to-machine communication essential for modern AI workflows.
The WireGuard Mesh Paradigm: The Scalability Crisis
Business Impact: The mathematical reality of mesh networks creates a hidden cost structure that escalates exponentially with growth. At 10,000 nodes, a full mesh theoretically requires 50 million connections—forcing expensive infrastructure upgrades, degraded performance, and delayed policy propagation that can take minutes or hours to synchronise across your network. For AI agent deployments where thousands of ephemeral identities spawn and terminate hourly, this architecture simply cannot function.
Technical Deep-Dive:
Solutions such as Tailscale and Netbird rely on the WireGuard protocol to establish encrypted data planes between participating devices. WireGuard is widely celebrated for its minimalistic codebase (fewer than 4,000 lines), high performance, and implementation of modern classical cryptographic primitives such as ChaCha20-Poly1305 for authenticated encryption and Curve25519 for elliptic-curve Diffie-Hellman key agreement. However, WireGuard is inherently designed for static, point-to-point connections, operating in a stateless manner that requires endpoints to have predefined knowledge of their peers' public keys and IP configurations.
To achieve zero-configuration mesh networking using a protocol designed for static tunnels, platforms like Tailscale and Netbird introduce a centralised coordination server acting as the control plane. This authority manages public key distribution, facilitates NAT traversal signaling (utilising STUN, TURN, or proprietary relay servers like Tailscale's DERP), and enforces access control lists (ACLs).
This hybrid architecture inevitably encounters the $O(n^2)$ state overhead problem. In a fully connected mesh network, required connections and cryptographic state grow quadratically with each new node. While access control policies can restrict connections to create a partial mesh, the centralised coordination server must still continuously synchronise reachability information, cryptographic states, and IP configurations across the entire fleet in real-time.
For human-centric organisations, this overhead manifests as database contention at the management plane, continuous background polling, and delayed state convergence. However, when applied to agentic AI—where tens of thousands of ephemeral machine identities may be instantiated, migrated, and destroyed hourly across distributed cloud environments—the static mesh paradigm collapses completely. The latency introduced by propagating ACL changes via centralised JSON files across globally distributed meshes renders these solutions inadequate for machine-speed operations.
Centralised Proxies: The Performance and Flexibility Bottleneck
Business Impact: Proxy-based ZTNA forces all traffic through centralised chokepoints, adding latency, creating single points of failure, and fundamentally blocking the bidirectional communication patterns required for modern AI agent orchestration. This architectural limitation creates an insurmountable barrier to AI transformation initiatives and forces expensive workarounds for machine-to-machine workflows.
Technical Deep-Dive:
Twingate eschews the peer-to-peer mesh model entirely in favour of a hybrid architecture utilising proprietary cloud-hosted control planes and localised network connectors. Rather than deploying full VPN protocols, Twingate relies on Transport Layer Security (TLS) proxying, creating logical access boundaries around specific internal applications rather than providing full network access. This approach excels in simplifying human-to-application access and integrates robustly with existing Identity Providers (IdPs) and Endpoint Detection and Response (EDR) telemetry.
Despite these operational advantages, the connector-based model introduces mandatory network chokepoints that degrade performance. Traffic must route from the client device, through cloud infrastructure or direct relays, into the localised connector before finally reaching the destination application. In legacy centralised architectures, public IPs are exposed via centralised controllers and relays, forcing client agents to traverse multiple intermediary hops to reach localised connectors, which then multiplex traffic to databases or APIs. This topology struggles profoundly with machine-to-machine communications operating within the same local area network or across highly distributed edge environments, lacking true peer-to-peer multi-hop capabilities.
Furthermore, proxy-style ZTNA suffers from two distinct operational limitations that severely impact agentic workflows:
First, explicit allow-lists drastically limit scalability. Proxy-based solutions rely on centralised control planes and explicit allow-lists (or rigid IP/DNS-based policies) to dictate which entities can access specific services. As enterprises expand to accommodate thousands of autonomous, ephemeral AI agents, continuous maintenance and synchronisation of these centralised allow-lists transform into massive operational bottlenecks. VeilNet addresses this by removing traditional proxies and achieving "Unbound Scalability," replacing explicit centralised allow-lists with decentralised micro-segmentation by identities, instantly evaluating connectivity directly between agent and service via cryptographic signatures.
Second, proxy ZTNA architectures are fundamentally designed around a reverse-proxy, client-initiated (ingress) model. These systems force strict unidirectional flow where connections originate solely from the client, route through centralised relays, and push down into backend services. However, in dynamic AI ecosystems, agents cannot operate as passive requesters. AI agents must frequently function as both clients and servers to receive asynchronous webhooks, execute peer-to-peer instructions, and manage complex multi-agent orchestration. Traditional proxy ZTNA natively blocks these server-initiated outbound flows back to the client, effectively severing bidirectional communication pathways essential for modern machine-to-machine operations.
Lastly, reliance on TLS over TCP inherently suffers from the well-documented "TCP-over-TCP" meltdown effect. When encapsulating dynamic, lossy workloads, stacking TCP congestion control mechanisms leads to unpredictable latency spikes, excessive retransmissions, and severe bufferbloat—conditions highly detrimental to high-throughput AI agent coordination requiring stable, jitter-free telemetry streams.
Competitive Comparison: VeilNet vs. Leading ZTNA Solutions
The following table systematically contrasts VeilNet's architectural approach with prevailing ZTNA platforms, highlighting the fundamental design differences that deliver superior scalability, security, and operational flexibility:
| Architectural Dimension | VeilNet | Tailscale & Netbird | Twingate |
|---|---|---|---|
| Network Topology | Ephemeral Non-Mesh (On-Demand) | Peer-to-Peer Static Mesh | Connector-Based Proxy |
| Routing Intelligence | Multi-Agent Reinforcement Learning | Static P2P with Cloud Relays (DERP) | Centralised Cloud Routing |
| Multi-Hop Capability | Native, Dynamic, Self-Healing | Limited (Requires Subnet Routers) | None (Point-to-Connector only) |
| Scalability Constraint | Linear (No $O(n^2) state overhead) | Degrades at scale (State sync bottlenecks) | Bound by explicit allow-lists |
| Communication Flow | Native Bidirectional (Client/Server) | Bidirectional | Client-Initiated Only |
| Configuration State | Zero Sync (Runtime Generation) | Centralised JSON ACL sync | Centralised Policy Sync |
| Underlying Protocol | Anchor Protocol (Non-IP) | WireGuard (IP-based) | TLS/TCP (IP-based) |
| Business Impact | cost reduction, increased performance when scaling up | Exponential infrastructure costs, degraded performance when scales up | Performance bottlenecks, limited AI use |
VeilNet's Breakthrough: Packet-Level Authentication
Traditional ZTNA solutions authenticate connections once during initial setup, then implicitly trust all subsequent traffic through that connection—creating a massive security blind spot. If a device or AI agent is compromised, attackers inherit full network access. VeilNet eliminates this vulnerability by verifying every single packet's cryptographic identity before allowing it onto the network, effectively creating a "virtual air gap" that contains breaches automatically. This reduces cyber insurance premiums, ensures regulatory compliance (NIST, ISO 27001), and prevents the lateral movement that transforms minor incidents into catastrophic breaches.
The Security Paradigm Shift:
The most critical vulnerability shared by traditional ZTNA architectures lies in their fundamental reliance on tunnel-level authentication. Whether utilising WireGuard, IPSec, or TLS-based connections, cryptographic identity validation occurs only during initial handshake and key exchange phases. Once the secure tunnel is established, the receiving firewall or software-defined perimeter inherently assumes all subsequent traffic emerging from that tunnel is legitimate, authorised, and benign.
This model directly violates core zero trust tenets by establishing a persistent perimeter of implicit trust within the tunnel itself. If an attacker—or a compromised autonomous AI agent—breaches a host machine, they automatically inherit the established cryptographic tunnel. The adversary can then freely inject malicious payloads, perform lateral network reconnaissance, or exfiltrate sensitive data. Because packets traverse a pre-authenticated tunnel, the receiving node accepts them as trusted traffic. Traditional security solutions attempt to mitigate this blind spot through application-layer firewalls and deep packet inspection, but these are inherently reactive measures detecting exploits only after the network boundary has been compromised.
How VeilNet's Packet Level Authentication Works
Technical Implementation:
VeilNet fundamentally resolves tunnel-level authentication vulnerabilities through implementation of Packet Level Authentication (PLA). Unlike WireGuard or TLS, which authenticate connection state, PLA enforces strict cryptographic identity verification on every single packet traversing the network before the receiving host's network stack ever processes it. This mechanism establishes the deepest access control achievable in modern networking, effectively creating a virtual air-gapped network.
Comparative analysis of authentication flows highlights PLA's superiority. In traditional Identity Provider (IdP) authentication models, the flow is highly sequential and prone to interception: an agent fetches credentials, sends a request containing those credentials to a service, the service relays credentials to an IdP for authorisation, and eventually a response is generated. This multi-step process leaves numerous vectors for credential harvesting and token theft.
VeilNet's PLA revolutionises this paradigm. The agent fetches cryptographic scopes directly from the IdP. Subsequently, every single communication between agent and target service is governed by Packet Level Authentication powered by post-quantum cryptography. If a packet contains a valid signature, connectivity is allowed; if the signature is invalid or missing, connectivity is immediately denied at the network layer, preventing the packet from ever reaching the application layer. This creates absolute micro-segmentation by identities. Even if one network segment is compromised, the lack of valid packet-level cryptographic signatures severs the lateral connection path, rendering the breach contained.
The Triple Factor Authentication Process:
In the VeilNet ecosystem, each Conflux node (the localised software connector interfacing with the network) generates a unique post-quantum cryptographic identity upon startup. When a node joins the network, it broadcasts its Dilithium Public Key and Conflux Signature as an immutable pair to the control channel, which all other participating nodes then store in local memory. For any packet to be accepted by a receiving node, it must pass rigorous Triple Factor Authentication (TFA) at the packet level:
- The digital signature and public key presented must perfectly match the immutable pair stored in the receiving node's local memory
- The signature must be perfectly reproducible using the key and specific signature embedded within the packet header
- The signature must mathematically validate when verified against the local key
Because VeilNet operates completely independently of conventional IP address subnets, attackers cannot utilise IP spoofing, port scanning, or traditional network reconnaissance techniques. Even if a host machine is completely compromised by an advanced persistent threat, the attacker cannot forge the post-quantum identity required to communicate with other protected services on the VeilNet overlay. Payload security is ensured via symmetric AES-GCM-256 encryption, utilising a shared secret negotiated via the Kyber Key Encapsulation Mechanism, which rotates automatically as frequently as every 15 seconds to ensure perfect forward secrecy.
Future-Proofing Your Security: Post-Quantum Cryptography
The emergence of quantum computing represents an existential threat to current encryption standards. Nation-state adversaries are already capturing encrypted traffic today with the intent to decrypt it once quantum computers mature—a strategy known as "Harvest Now, Decrypt Later." Federal mandates (CNSA 2.0) require quantum-resistant encryption by 2026, with legacy systems phased out by 2030. Organisations that delay this transition face regulatory non-compliance, uninsurable cyber risk, and potential exposure of sensitive data captured years earlier. VeilNet provides immediate quantum-readiness, protecting your organisation's long-term confidentiality and ensuring compliance with evolving federal security standards.
The Quantum Threat Timeline:
The inevitability of cryptographically relevant quantum computers poses an existential threat to classical asymmetric algorithms—such as Rivest-Shamir-Adleman (RSA) and Elliptic Curve Cryptography (ECC)—that currently secure the global internet. These algorithms form the cryptographic backbone of almost all current ZTNA key exchanges and digital signatures. In response to the highly publicised "Harvest Now, Decrypt Later" (HNDL) threat model—where nation-state adversaries capture encrypted traffic today with explicit intent to decrypt it once quantum hardware matures—national security agencies and standard-setting bodies worldwide have mandated rapid, industry-wide transition to Post-Quantum Cryptography.
Global Regulatory Mandates:
Multiple jurisdictions have established formal quantum-readiness timelines with enforceable compliance requirements:
- United States: The NSA's Commercial National Security Algorithm Suite 2.0 (CNSA 2.0) requires traditional networking equipment like VPNs and routers to support quantum-resistant algorithms by 2026, with all legacy systems phased out entirely by 2030.
- European Union: The EU Commission Recommendation 2024/1101 establishes a coordinated PQC implementation roadmap requiring Member States to initiate national PQC strategies by end of 2026, mandate high-risk systems (critical infrastructure, telecommunications, finance, government) to complete PQC transition by 2030, and achieve comprehensive PQC deployment across all feasible systems by 2035. The NIS2 Directive (2022/2555) further codifies cryptographic risk management obligations that explicitly encompass quantum threats, making PQC transition an auditable compliance requirement for essential and important entities.
- Australia: The Australian Signals Directorate (ASD) through the Australian Cyber Security Centre (ACSC) mandates organisations develop detailed PQC transition plans by end of 2026, begin implementation of quantum-resistant cryptography in critical systems by end of 2028, and complete full transition by 2030.
Despite these converging global mandates, legacy VPN providers face severe engineering hurdles in adopting PQC natively due to massive computational and bandwidth overhead associated with quantum-resistant mathematics.
VeilNet's Implementation: NIST-Standardised Quantum-Resistant Algorithms
Technical Implementation:
VeilNet bypasses legacy constraints by integrating finalised National Institute of Standards and Technology (NIST) PQC standards directly into its foundational data plane from inception. For secure key encapsulation and exchange, VeilNet utilises CRYSTALS-Kyber, officially standardised by NIST as ML-KEM under FIPS 203. Kyber relies on the computational hardness of the Module Learning with Errors (MLWE) problem over algebraic lattices. Unlike classical cryptographic algorithms relying on the difficulty of integer factorization or calculating discrete logarithms, lattice-based cryptography introduces intentional mathematical noise (errors) into linear equations. This structural complexity makes equations unsolvable even by Shor's algorithm operating on sophisticated quantum computers.
For robust identity verification and absolute non-repudiation, VeilNet implements CRYSTALS-Dilithium, standardised by NIST as ML-DSA under FIPS 204. Dilithium provides strongly unforgeable digital signatures based on the Fiat-Shamir with Aborts framework applied to module lattices.
Overcoming the Performance Challenge:
While lattice-based algorithms offer unparalleled future-proof security, they inherently require significantly larger key sizes and generate much larger ciphertexts than classical counterparts. As illustrated in the cryptographic comparison below, ML-DSA-256 (providing security equivalent to AES-256) produces signatures of approximately 3,309 bytes. In traditional networking environments, appending a 3,309-byte signature to standard datagrams forces UDP-based transports into inefficient IP packet fragmentation. Fragmentation introduces severe reliability issues, increased latency, and requires complex reassembly logic that degrades overall network throughput.
| Cryptographic Algorithm | Security Level Target | Encapsulation Key (Bytes) | Decapsulation Key (Bytes) | Ciphertext/Signature Size (Bytes) |
|---|---|---|---|---|
| Classical RSA-3072 | 128-bit equivalent | 387 | 384 | — |
| Classical RSA-15360 | 256-bit equivalent | 1,947 | 1,944 | — |
| Classical ECC (Curve25519) | 128-bit equivalent | 32 | 32 | 32 |
| Classical ECC (Curve448) | 224-bit equivalent | 56 | 56 | 56 |
| ML-KEM-512 (Kyber) | 128-bit equivalent | 800 | 1,632 | 768 |
| ML-KEM-768 (Kyber) | 192-bit equivalent | 1,184 | 2,400 | 1,088 |
| ML-KEM-1024 (Kyber) | 256-bit equivalent | 1,568 | 3,168 | 1,568 |
| ML-DSA-128 (Dilithium) | 128-bit equivalent | 1,312 (Public Key) | 2,560 (Private Key) | 2,420 |
| ML-DSA-256 (Dilithium) | 256-bit equivalent | 1,952 (Public Key) | 4,032 (Private Key) | 3,309 |
VeilNet entirely resolves this computational and bandwidth overhead through its proprietary architectural design. By operating as an independent, non-IP network layer, VeilNet completely circumvents strict Maximum Transmission Unit (MTU) penalties and fragmentation limits associated with traditional VPN encapsulation. The network achieves sub-millisecond cryptographic overhead by utilising highly optimised AES-GCM-256 for symmetric payload encryption, combined with bespoke implementation of ML-KEM-1024 (Kyber) and ML-DSA-256 (Dilithium) at 256-bit equivalent security. Independent network performance benchmarks indicate that optimised lattice-based KEMs like Kyber consistently deliver superior performance in handshake stability and connection resumption compared to legacy algorithms, particularly under high-latency or degraded link conditions.
The VeilNet Architecture: Self-Healing Networks Through AI
VeilNet eliminates the exponential scaling costs of mesh networks through intelligent, on-demand networking. Rather than maintaining millions of pre-configured connections, VeilNet creates secure pathways only when needed, automatically routing around failures and network congestion in real-time. This architecture ensures uptime without expensive redundant infrastructure, reduces bandwidth costs by eliminating unnecessary connection overhead, and scales linearly—meaning your 10,000th node costs the same to add as your 100th. The system uses Multi-Agent Reinforcement Learning to continuously optimise routing, self-heal from outages, and adapt to changing network conditions without manual intervention. Performance and reliability increases with your infrastructure scale, instead of degradation.
Technical Architecture Overview:
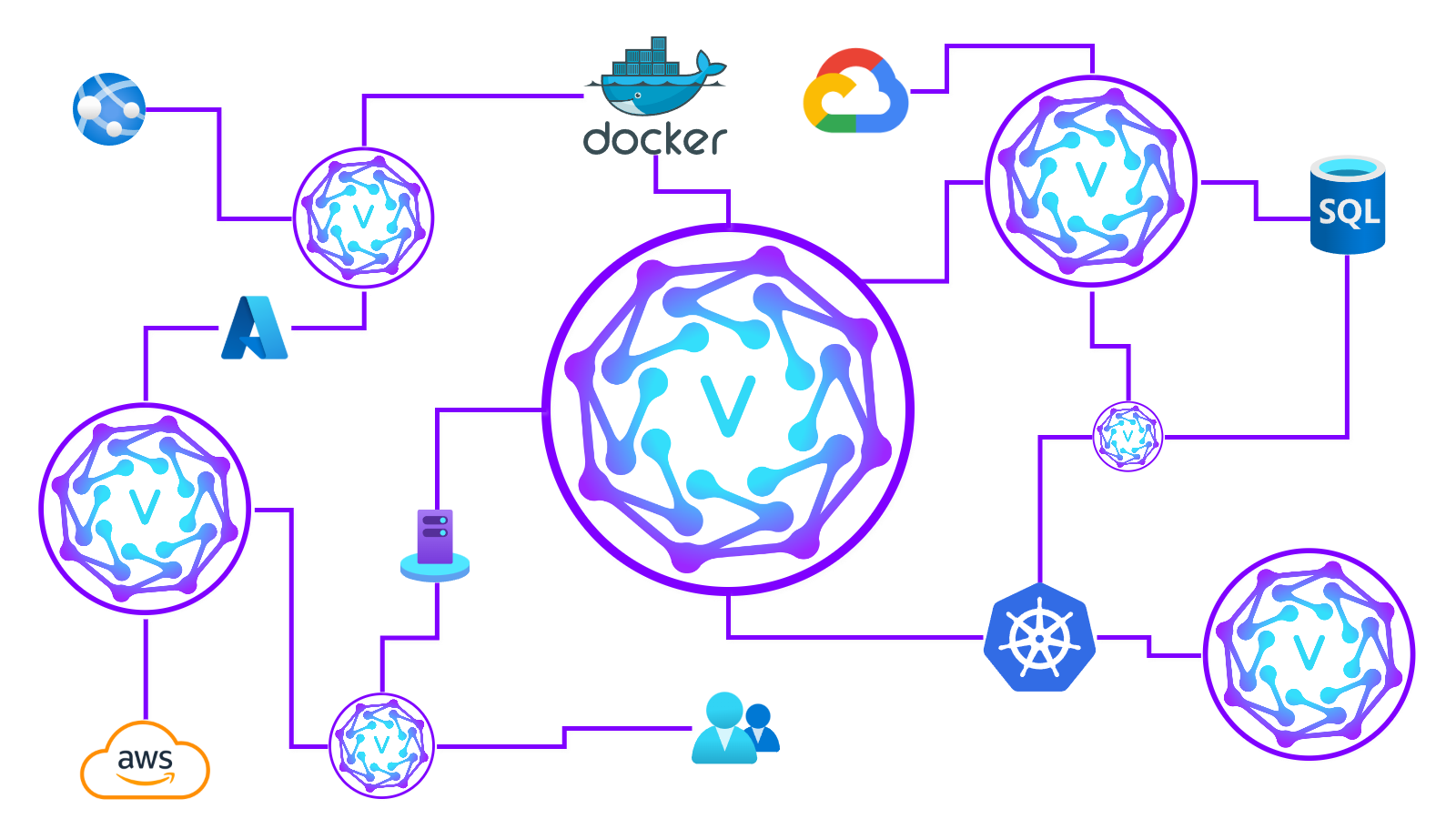
To definitively overcome the $O(n^2)$ scaling limitations of traditional mesh VPNs, VeilNet eliminates static network topologies entirely through deployment of its proprietary Anchor Protocol. The VeilNet architecture comprises three highly specialised, distinct components operating in unison to provide a decentralised, ephemeral networking fabric:
- VeilNet Master — Functions as a high-performance NATS super-cluster. Crucially, the Master acts purely as a control-channel message broker; it does not route data payloads, nor does it hold decryption keys.
- VeilNet Guardian — Serves as the centralised authentication and identity server. The Guardian leverages robust OAuth2 integrations and issues JSON Web Tokens (JWTs) with both long-lived and short-lived lifespans to strictly govern node identities.
- VeilNet Conflux — The decentralised software edge node running on virtual machines, physical hardware, or as containerised sidecars to form the active data plane of the network.
A standard Conflux Node incorporates a Virtual Kernel containing specialised DNS and DHCP services, alongside a Virtual SD WAN module. This internal architecture ensure absolute network isolation even on the host. Traffic flows from underlying hardware, through the OS kernel into a TUN interface, and is then securely managed by the Conflux via Anchor Protocol. This decentralised design allows individual nodes to communicate securely via packet-level authentication without routing payload data through a central, monolithic controller.
Intelligent Routing: Multi-Agent Reinforcement Learning
How AI Powers Self-Healing Networks:
VeilNet is fundamentally non-mesh and purely ephemeral. Nodes do not download global configuration files, complex routing tables, or static peer lists, ensuring configuration state remains dynamic. Instead, secure data channels are instantiated entirely on-demand and dissolve immediately when idle. When a Conflux node needs to transmit a packet, it spawns an "egresser" process utilising the NATS control channel to instantaneously discover a route.
This route discovery mechanism represents a category-defining advancement, driven by a Multi-Agent Reinforcement Learning (MARL) algorithm embedded directly within the Anchor Protocol. Traditional routing protocols, such as Open Shortest Path First (OSPF), utilise static algorithms like Dijkstra's to calculate paths based on rigid link weights. These static approaches are fundamentally incapable of reacting to micro-fluctuations in network state, packet loss, or latency jitter, making them unsuitable for dynamic wireless environments or globally distributed cloud infrastructures.
By contrast, routing in VeilNet's highly dynamic, multi-hop environment is mathematically structured as a Markov Decision Process (MDP). Each Conflux routing node acts as an independent intelligent agent, continuously evaluating conflicting environmental variables such as link latency, throughput capacity, and historical node reliability. VeilNet's Anchor Protocol utilises a unified, highly efficient Multi-Armed Bandit (MAB) EXP3 algorithm.
Operational Benefits:
This MARL model allows Conflux nodes to cooperatively learn and predict the most efficient multi-hop routes across the global fabric in real-time. Once the optimal path is mathematically verified, the originating node establishes a "tether"—a logical, encrypted aggregation of WebRTC data channels—to the next hop. This allows VeilNet to seamlessly route traffic directly between peers, or optimally bounce traffic across intermediate nodes to bypass strict enterprise firewalls or Carrier-Grade NAT (CGNAT) restrictions. If an intermediate node fails, the reinforcement learning algorithm instantly degrades the reward value of that path, causing the network to autonomously self-heal and route traffic around localised outages without dropping the connection.
This self-healing capability translates directly to business continuity: networks remain operational during infrastructure failures, maintenance windows occur without service disruption, and network performance continuously improves as the AI learns optimal routing patterns for your specific traffic patterns.
Use Case: Securing AI Agent Ecosystems
By 2026, AI agents will outnumber human workers 82 to 1. Traditional ZTNA and IAM systems designed for human users cannot scale to secure millions of ephemeral, high-velocity machine identities. VeilNet provides the foundational security layer for AI transformation initiatives, enabling safe deployment of autonomous agents while preventing the catastrophic breach scenarios (prompt injection, privilege escalation, lateral movement) that could expose sensitive corporate data or disrupt business operations. This capability is essential for organisations pursuing AI-driven efficiency gains while maintaining acceptable risk levels.
The Agentic AI Challenge:
The technological transition from conversational generative AI chatbots to autonomous, agentic AI represents a fundamental restructuring of computing architecture. Unlike reactive language models requiring constant human prompting, AI agents perceive digital environments, autonomously formulate complex multi-step plans, interact with disparate enterprise APIs, and manipulate real-world corporate data without human intervention. Consequently, underlying network infrastructure ceases to be a mere conduit for human web traffic; it transforms into the foundational trust layer necessary for machine-to-machine (M2M) operational execution.
Market analysts forecast that by 2026, autonomous digital agents will outnumber human workers by an astonishing ratio of 82 to 1. Traditional ZTNA platforms and Identity and Access Management (IAM) frameworks—which were inherently designed to manage human users with static roles, biometrics, and persistent sessions—are structurally incapable of securing the millions of ephemeral, high-velocity non-human identities generated by agentic workflows.
Application: Securing the Model Context Protocol (MCP)
Business Value: The Model Context Protocol enables AI agents to access corporate databases, tools, and sensitive information. Without proper security, compromised agents can exfiltrate confidential data, manipulate financial records, or pivot to unauthorised systems. VeilNet's microsegmentation ensures each agent can only access explicitly authorised resources—even if compromised, the agent cannot move laterally to attack other systems. This enables safe AI adoption while maintaining zero-trust security posture.
Technical Implementation:
As enterprise software architecture evolves toward "digital assembly lines," multiple highly specialised AI agents must continuously collaborate to execute complex, end-to-end business logic. This advanced orchestration is increasingly facilitated by the Model Context Protocol (MCP), an emerging open-source standardisation that securely exposes local enterprise data sources, internal databases, and bespoke tools directly to AI reasoning engines. Securing MCP is paramount for enterprise safety, as it acts as the literal bridge between raw algorithmic intelligence and actionable, sensitive corporate data.
The proliferation of agentic workflows introduces severe, unprecedented threat vectors. Chief among these is the threat of prompt injection resulting in "excessive agency" or unauthorised privilege escalation. If an AI agent tasked with benign public data aggregation is compromised via adversarial prompt injection attack, it may autonomously pivot operations to exfiltrate sensitive corporate telemetry. Traditional proxy gateways (such as NGINX or Envoy) lack deep context-awareness required to differentiate between legitimate multi-agent tool calls and malicious payload injection initiated by hijacked agents. In legacy perimeter models or WireGuard mesh networks, compromised agents inherit broad network trust associated with their host machine, rendering lateral movement trivial and entirely invisible to standard firewalls.
VeilNet's Solution:
VeilNet directly mitigates this crisis through workflow microsegmentation enforced by Packet Level Authentication. By deploying VeilNet Conflux instances as sidecars alongside MCP servers and orchestrator agents, enterprises establish an impenetrable zero-trust fabric tailored specifically for agentic communication. By integrating the VeilNet SDK directly into the agent's runtime environment, the agent is assigned a cryptographically verifiable, post-quantum identity.
Access is subsequently defined by rigid, default-deny network policies at the identity level. For example, a policy may dictate that "Research Agent Alpha is strictly permitted to establish a stream with Database Beta, and no other entity." If the compromised agent attempts to initiate an unauthorised connection to a human resources server, the request is not dropped by a firewall evaluating IP addresses; rather, the packet is fundamentally rejected by the destination host's Conflux node because it lacks the valid Dilithium signature required for that specific microsegmented pathway. This architecture severs the lateral connection path visually and functionally, enforcing perfect least-privilege architecture at the deepest achievable network layer.
Application: Autonomous Financial and Supply Chain Systems
Business Value: High-frequency trading, algorithmic financial operations, and real-time supply chain logistics cannot tolerate network failures or latency spikes. Traditional ZTNA solutions lack the resilience and performance required for these mission-critical applications. VeilNet's self-healing architecture and quantum-resistant encryption protect high-value financial data from future quantum attacks while ensuring continuous sub-millisecond execution even during infrastructure outages. This enables organisations to deploy autonomous financial systems with acceptable risk levels and regulatory compliance.
Technical Implementation:
The integration of agentic AI into high-stakes, mission-critical environments—such as decentralised finance (DeFi), algorithmic trading, and global supply chain logistics—demands network resilience levels that simply cannot be guaranteed by static mesh topologies. In these sectors, AI agents execute thousands of sub-cent micro-operations per second, reacting dynamically to volatile market conditions or autonomous edge-sensor telemetry. Network failures, latency spikes, or state-synchronisation delays across traditional mesh VPNs can result in catastrophic financial loss or cascading supply chain disruption.
Furthermore, high-frequency financial telemetry is the primary target for quantum-equipped adversaries employing "Harvest Now, Decrypt Later" strategies. Relying on classical TLS or WireGuard tunnels exposes this high-value data to certain future decryption, violating emerging regulatory mandates for quantum readiness in the financial sector.
VeilNet's Solution:
VeilNet provides critical, future-proof infrastructure required for autonomous financial execution. As transaction agents route capital across highly distributed cloud environments, VeilNet's Kyber KEM and AES-GCM-256 encryption ensure absolute mathematical confidentiality of transaction data against any form of quantum interception. Simultaneously, the Anchor Protocol's Multi-Agent Reinforcement Learning algorithm continuously analyses global network state. If an intermediate ISP routing node experiences degradation, or a specific cloud region suffers unexpected outage, the RL algorithm autonomously predicts the failure and reroutes the encrypted tether through an optimal secondary path in real-time. This self-healing capability guarantees continuous, sub-millisecond execution for agents, operating entirely independently of manual human network intervention, rigid BGP configurations, or fragile DNS failovers.
AI Agent Security: Comprehensive Threat Mitigation
The following table aligns MITRE ATLAS and OWASP LLM vulnerabilities with VeilNet's specific architectural defences, demonstrating comprehensive protection against emerging AI-specific threats:
| Agentic Threat Vector (OWASP / MITRE ATLAS) | Traditional ZTNA Vulnerability | VeilNet Architectural Defense | Business Impact |
|---|---|---|---|
| Prompt Injection / Excessive Agency | Agent inherits host machine's broad network access | PLA enforces strict, per-packet microsegmentation | Prevents data exfiltration and lateral movement |
| Credential & Token Compromise | Stolen API keys or long-lived JWTs grant persistent access | Cryptographic post-quantum ID tied to Ephemeral Streams | Eliminates credential theft as attack vector |
| Lateral Movement / Reconnaissance | Implicit trust within established WireGuard/TLS tunnel | Virtual air-gap; packets rejected without Dilithium signatures | Contains breaches, prevents cascade failures |
| Harvest Now, Decrypt Later (HNDL) | Classical Curve25519 or RSA encryption easily stored | ML-KEM (Kyber) and ML-DSA (Dilithium) render interception useless | Protects long-term data confidentiality |
| Denial of Service via Subnet Discovery | Static IPs and centralised gateways can be targeted | Non-IP network; topology is invisible and ephemeral | Maintains business continuity under attack |
Use Case: Modernising Traditional Enterprise Infrastructure
Modern enterprises maintain expensive, fragmented arrays of VPNs, proxies, service meshes, secure web gateways, and complex firewalls—each requiring separate management, licensing, and expertise. VeilNet consolidates this entire stack into a single unified platform, reducing infrastructure costs by 30%, eliminating configuration complexity, and dramatically reducing attack surface. Organisations achieve immediate ROI through reduced licensing fees, lower administrative overhead, and simplified compliance auditing across a unified security architecture.
The Legacy Infrastructure Challenge:
While VeilNet has been structurally optimised to handle extreme rigors of agentic AI, its profound architectural innovations offer significant advantages for modernisation of traditional enterprise IT infrastructures. Modern enterprises are burdened by immense technical debt, forced to maintain fragmented arrays of VPN concentrators, external reverse proxies, internal service meshes, secure web gateways, and complex, overlapping firewall rule sets. VeilNet acts as a unifying overlay, collapsing this legacy network stack into a single, cohesive, identity-driven platform.
Application: Infrastructure Consolidation and Stack Simplification
Business Impact: Traditional application delivery requires traffic to traverse CDNs, load balancers, multiple proxies, VPN gateways, and service meshes—each hop adding latency, cost, and security risk. VeilNet eliminates this entire chain, reducing infrastructure costs by 30%, improving application performance, and dramatically reducing attack surface. Each eliminated component represents saved licensing fees, reduced administrative overhead, and fewer potential security vulnerabilities.
Technical Implementation:
The complexity of traditional application delivery creates a fragile and expensive operational environment. Standard enterprise requests typically traverse a public IP, pass through a Content Delivery Network (CDN), hit centralised load balancers, route through multiple proxy servers, enter VPN gateways, and finally navigate internal service meshes before reaching designated microservices. Each hop introduces latency, requires independent configuration management, and expands external attack surface.
VeilNet dramatically simplifies this convoluted tech stack. By deploying VeilNet, enterprises can bypass CDNs, load balancers, traditional proxies, VPNs, and complex service meshes entirely. Instead, a public IP connects to the full stack application, which then utilises a VeilNet Virtual IP to communicate directly and securely with highly interconnected backend services. This consolidation ensures reliable connectivity, unbound scalability, and vastly superior security, as attack surface is reduced to a single, mathematically verified point of entry.
Eliminating IP-Centric Complexity:
Traditional enterprise network security relies heavily on Network Access Control (NAC) systems and perimeter firewalls inextricably bound to static IP addresses, subnets, and VLANs. This IP-centric paradigm collapses in the face of hybrid remote workforces, multi-cloud deployments, and dynamic container orchestration platforms like Kubernetes, where IP addresses are ephemeral and physical location is irrelevant. Administrators are forced to continually modify complex ACLs and route advertisements, leading to inevitable misconfigurations, routing loops, and critical security gaps.
VeilNet abstracts underlying physical and virtual network topologies entirely. Because the Anchor Protocol routes traffic based on verified cryptographic identity rather than fragile IP addresses, VeilNet operates seamlessly across bare-metal servers, hypervisors, and container runtimes without requiring auxiliary sub-routers, NAT traversal modifications, or manual IP routing updates. Deployment of a single VeilNet Conflux instance within a legacy data centre grants instant, full-stack access to authorised users and services globally, explicitly bypassing the need to expose public-facing VPN gateways or maintain vulnerable Demilitarised Zones (DMZs).
Application: Hybrid-Cloud Migration and Legacy OT Security
Business Value: Migrating applications between on-premises data centres and multi-cloud environments traditionally requires months of coordination, expensive SD-WAN implementations, and complex BGP/firewall configurations. VeilNet enables instant secure connectivity across heterogeneous environments without network re-architecture, accelerating cloud migrations by 75% while maintaining zero-trust security. Additionally, VeilNet secures legacy industrial control systems (SCADA, PLCs) that cannot be upgraded or patched, protecting critical infrastructure from cyber attacks without replacing operational technology hardware.
Cloud Migration Simplified:
Consider a multinational enterprise tasked with migrating critical, monolithic applications from aging on-premises data centres to distributed multi-cloud environments spanning AWS and Azure. Utilising traditional SD-WAN or IPsec VPNs for this migration requires extensive, error-prone coordination between network engineers to establish BGP peering, configure non-overlapping CIDR blocks, and manage complex firewall ingress and egress rules. This process is inherently brittle, highly expensive, and scales poorly as new regions are added. Furthermore, once employees or contractors connect to corporate VPNs, they are frequently granted broad, over-privileged access to entire flat networks, fundamentally violating zero trust principles.
By deploying VeilNet, enterprises achieve instant, secure network modernisation without massive re-architecture overhead. VeilNet Conflux nodes are seamlessly installed as software services alongside legacy applications in on-premises data centres, as well as within cloud VPCs. Employees authenticate via the company's existing Identity Provider (such as Okta, Google, or Microsoft Entra ID). Rather than granting network-wide IP access based on successful login, enterprises utilise VeilNet's Team and Realm configurations to assign strict, identity-based affinity rules.
Under this model, an accountant accessing a legacy financial database establishes a direct, post-quantum encrypted stream to that specific server, while remaining completely network-isolated from cloud-hosted HR applications or engineering testbeds. Because VeilNet functions as an ephemeral, non-mesh overlay, enterprises avert the configuration of complex JSON policies required by platforms like Tailscale, achieving global, granular connectivity without modifying a single legacy firewall rule.
Securing Legacy Operational Technology:
This capability extends powerfully into the realm of Operational Technology (OT). Industrial environments and critical infrastructure often rely on legacy Supervisory Control and Data Acquisition (SCADA) systems that run outdated, unpatchable operating systems and utilise cleartext communication protocols like Modbus. These systems lack hardware resources to support modern cryptographic agents.
VeilNet provides an elegant, non-intrusive security overlay for these vulnerable OT environments. By deploying VeilNet Conflux instances on industrial gateways situated physically adjacent to legacy machinery, organisations establish secure, post-quantum enclaves. The Conflux node acts as an identity-aware proxy for legacy equipment. When remote engineers require access to Programmable Logic Controllers (PLCs) for emergency maintenance, their authenticated traffic is routed via the VeilNet fabric, protected by Dilithium signatures across the public internet. Upon reaching the localised Conflux node within the industrial facility, packets are authenticated via PLA, decrypted, and safely passed to legacy PLCs over local isolated segments. This architecture effectively shields inherently insecure equipment from lateral movement, unauthorised access, and quantum interception, fulfilling strict Zero Trust Architecture mandates without requiring costly modifications to underlying legacy code or industrial hardware.
Conclusion: The Strategic Imperative for VeilNet
Executive Summary:
The enterprise network security landscape is undergoing fundamental transformation driven by three irreversible trends: the exponential proliferation of autonomous AI agents, the imminent threat of quantum computing, and the proven inadequacy of traditional ZTNA architectures to scale effectively. Organisations that delay addressing these challenges face compounding risks: regulatory non-compliance with emerging federal quantum mandates (CNSA 2.0), inability to deploy AI transformation initiatives safely, and escalating infrastructure costs as legacy mesh networks degrade under scale pressure.
VeilNet delivers immediate, measurable business value:
- Infrastructure cost reduction through elimination of redundant security products (VPNs, proxies, service meshes, complex firewall management)
- Faster deployment enabling rapid cloud migrations and AI initiative launches
- Improved system availability via self-healing architecture that automatically routes around failures
- Future-proof security investment meeting federal quantum-resistance mandates ahead of 2026 compliance deadlines
- Linear scaling complexity supports unlimited growth without exponential cost penalties
- Reduced cyber insurance premiums through demonstrable zero-trust implementation and quantum-resistant encryption
Technical Foundation:
The comprehensive comparative analysis within this report demonstrates that while contemporary mesh networks and proxy-based ZTNA solutions successfully abstract configuration complexities of legacy VPNs, they remain inextricably tethered to outdated operational paradigms. Their reliance on tunnel-level trust, vulnerable classical cryptography, and centralised state synchronisation ensures they will degrade at scale and remain vulnerable to both advanced persistent threats and future quantum decryption.
VeilNet comprehensively transcends these limitations. By engineering a novel network architecture that integrates Post-Quantum Cryptography (ML-KEM and ML-DSA), Packet Level Authentication (PLA), and a self-organizing, reinforcement learning-driven routing protocol (Anchor Protocol), VeilNet offers an unprecedented convergence of absolute security, high performance, and linear scalability.
Strategic Positioning:
Whether deployed to secure intricate, multi-agent orchestration of autonomous AI workflows, or to seamlessly consolidate and modernise fragile legacy hybrid-cloud infrastructures, VeilNet operates not merely as a connectivity tool, but as an impenetrable cryptographic trust fabric. As global organisations navigate immense complexities and risks of the agentic era, transitioning from reactive, IP-based network defences to VeilNet's proactive, identity-driven packet authentication represents a strategic, non-negotiable imperative for ensuring continuous, resilient, and quantum-safe operational execution through 2026 and beyond.
Next Steps:
Organisations evaluating VeilNet should consider:
- Assessment Phase: Evaluate current ZTNA infrastructure costs, scalability limitations, and quantum-readiness gaps
- Pilot Deployment: Implement VeilNet for specific high-value use cases (AI agent security, critical infrastructure protection, or cloud migration initiatives)
- ROI Validation: Measure infrastructure cost reductions, deployment time improvements, and security posture enhancements
- Expansion: Scale VeilNet deployment across enterprise environments, systematically retiring legacy VPN and ZTNA infrastructure
VeilNet represents not an incremental improvement to existing ZTNA solutions, but a fundamental architectural breakthrough that addresses the converging security challenges of the next decade. Organisations that recognise and act on this paradigm shift will establish defensible competitive advantages through superior security posture, operational efficiency, and AI-enablement capabilities.


